According to Statista, cloud computing has taken over the globe generating billions of dollars of revenue. The graph keeps going up and won’t be slowing down any time. It is due to obvious reasons. Cloud computing has seen better management of data and easy access, giving it an edge over traditional methods of data management.
A Quick History of Cloud Computing
The question, however, is how safe is cloud data? Well, the safety of data regardless of whether it is stored in the cloud or locally on tapes is in your hands. Your cloud data is faced with many risks such as insider threats, loss of sensitive data, hacking and abuse of cloud services. Combined with MySQL backup, the following cloud data security practices will go a long way in simplifying your data backup processes and at the same time ensure that your data is secure.
Have local backup

Why Small Businesses Need To Take Their Security Seriously
Better safe than sorry. You cannot solely depend on cloud backup. What if it gets lost or corrupted? It is for this reason that backing your data locally is emphasized. It does not matter whether the data will be in the form of electronic copies or stores in external storage. You need to have access to your data regardless of whether the one stored in the cloud is available or not. Remember that sometime there might be a poor internet connection. What that means is that there is not much you can do with the data stored in the cloud. You will need an alternative at this point.
Encrypt data

It’s Time To Go Into Security Overdrive!
There are several cloud data services in the market. However, not all will encrypt your data. Why do you need to encrypt your data? Your data is not entirely safe when on the cloud. Note that service providers can be able to access it at any given time. To ward off this setback, it is crucial that you have your data encrypted. An extra layer of protection will not hurt: that is what encryption will offer you.
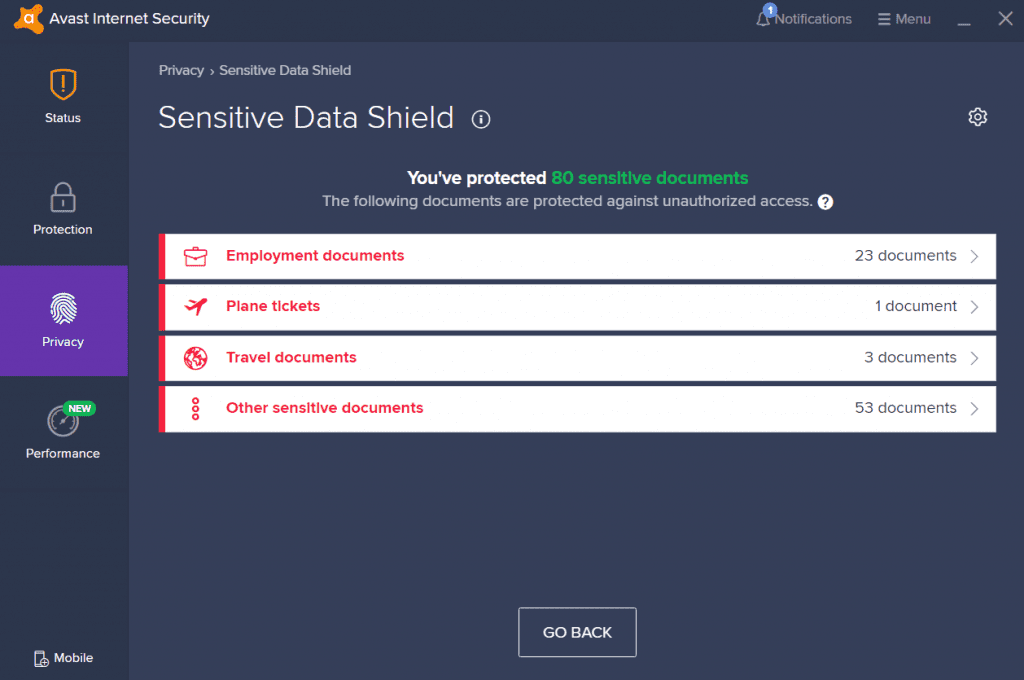
Get an anti-virus software

3 Cloud Backup Solutions For WordPress Blogs
Hackers can be quite a nuisance. Reports show that Microsoft has over 1 million breach attempts on data every day. That means that hackers are a growing concern and you should keep them away from your data. Among the most effective ways of mitigating this problem is by using anti-virus software. Not implementing security measures makes you an easy target to the hackers. Note that viruses are one of the entry points of hackers.
Use stronger passwords
Using simple passwords can be tempting. When it comes to cloud data security, you cannot afford to gamble with this. Passwords also provide you with an extra layer of protection and will ensure that hackers and other intruders do not have the easiest of time accessing your data. Your passwords should be unique: simple and apparent passwords will give hackers an easy way in. Also, remember to regularly change them and be careful with who you share them with.
Do not store sensitive information
5 Apps That Protect You From Hackers
Is there information that you deem very sensitive and could cause you great losses if tampered with? It is better that you do not store it in the cloud. There is so much cybercrime, and the safety of your data can never be guaranteed. There is some information that you should, by all means, avoid keeping on the internet that is passwords and information regarding your debit and credit cards. This information could land in the wrong hands and hurt you and your organization significantly.
Get a virtual private cloud

Worried About Data Security? Use a Cloud Service!
Did you know that it is possible for you to request your SaaS provider to create for you a cloud environment that only you has complete control over? Well, now you know. You can never trust anyone, and that includes your provider. By having full control over your cloud data, you get the additional assurance that your data will not land in the wrong hands.
Have a data deletion policy
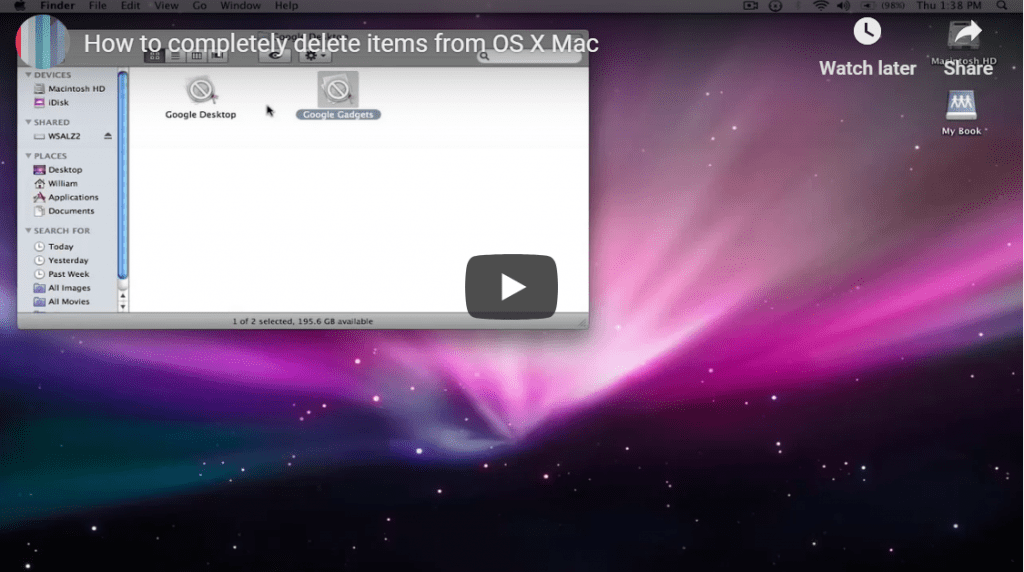
Is It Really Gone? Why You Need To Securely Delete For Data Elimination On Mac
If you do not want your company to get in trouble for leaked customer information, it is advisable to reduce the risk by doing away with some of your customer’s data especially if you have already closed business with them. Have a defined system that automatically deletes customer information once your contract has come to an end. You do not want to get into trouble for information that you are not even using, more so, you will create more space for new clients.
Test and test!

4 Reasons Why Penetration Testing Is Crucial to Your IT Infrastructure
You need to continually test whether the security measures you have put in place are at all practical. One effective way of going about it is by employing the services of certified and ethical hackers who could try and hack your cloud storage to test how strong your security is. If they can access your data, then that raises red flags. It only means that someone else would easily do if they attempted.
The advantages that cloud data storage comes with cannot be ignored. They are immense. However, it is also vital to note that cloud data storage too is faced by several risks. The mentioned practices will come in handy in ensuring that your data is safe at all times.