With the rise in technology, a lot is changing in the world. People are going digital, be it with their client list or their banking process. You can now sit at your friend’s neighbor’s basement dealing in business, and as long as the client’s happy, no one is the wiser. The world is just a click away.
With such ease comes a lot of looking behind your metaphorical shoulder every minute. No one is safe anymore. Cybersecurity is something that is a long lost dream. Multi-million dollar companies spend billions of dollars annually on their cybersecurity, yet they too at times fall victim to phishing. Cybersecurity is a serious issue, one that has to be taken seriously since the start.
Cyber security is a complex and ever-evolving field, and it can be difficult to keep up with the latest threats. But there are a few common pitfalls that can make you more vulnerable to attack.
Here are some basic cyber security issues you can easily prevent:
- Using weak passwords. Weak passwords are one of the easiest ways to get hacked. If your password is easy to guess, a hacker can easily gain access to your account.
- Not using two-factor authentication. Two-factor authentication adds an extra layer of security to your account by requiring you to enter a code from your phone in addition to your password. This makes it much more difficult for hackers to gain access to your account.
- Clicking on links in emails from unknown senders. Emails from unknown senders are often used to spread malware or phishing scams. If you click on a link in an email from an unknown sender, you could be infected with malware or tricked into giving away your personal information.
- Not keeping your software up to date. Software updates often include security patches that can protect you from known vulnerabilities. If you don’t keep your software up to date, you could be leaving your system vulnerable to attack.
- Storing sensitive information on your computer or phone. If you store sensitive information on your computer or phone, such as your credit card number or Social Security number, make sure to encrypt it. This will make it much more difficult for hackers to steal your information.
By avoiding these basic cyber security mistakes, you can help to protect yourself from attack. So please, take a few minutes to learn about the following pitfalls and how to avoid them. Your security depends on it.
The Following are the handful of most common pitfall that one may face if they do not take care and properly deal with their cybersecurity:
We are at the initial stages
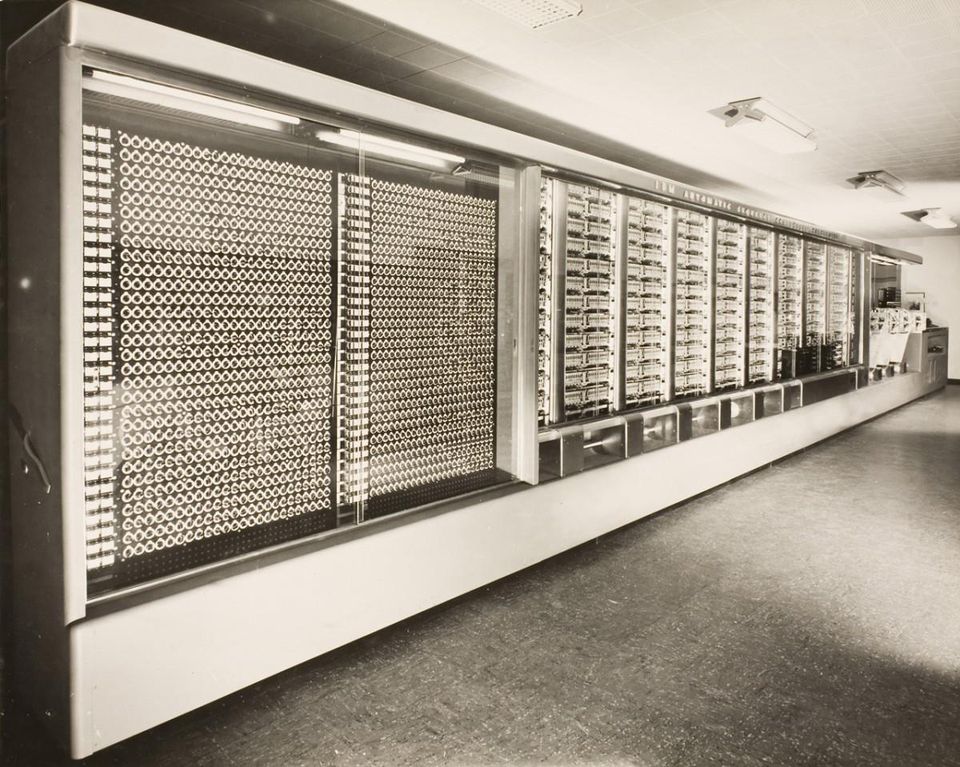
This Week In Tech History: The Birth Of The Cybersecurity And Computer Industries
No one is too small. Dismissing the idea of investing in cybersecurity because your firm is at its initial stages or because you are not that well-known is just playing with your client’s well-placed trust. It is, in fact, the first step to losing your future business.
Though it is true that phishers do not breach your security overnight, it takes long and meticulous planning and a slight sloppy employer or employee to do the deed.
It is also true that anyone can be baited at any time of their business life. No one can predict when they can be baited. It is better to invest smartly in cybersecurity and keep one’s nose down.
We are secure

The state of cyber security: we’re all screwed
Just like a doctor has to be updated with cutting-edge treatment and medicines being discovered every day, cybersecurity is something that needs to be updated frequently too.
As the era is changing on a much faster pace and more advanced things are being released in the market, any company cannot just spend a decent amount of money on cybersecurity once and be done with it. They have to have a team to keep a check on things to see if they are not breached and to see if their walls are still up and running.
Being stagnant with your ideas and leaving the security checkpoints the same for days on end is highly damaging. Companies should spend well not only on implementing cyber security but must also keep a check on it as well.
Humans – the weaker link

Lance Spitzner: How To Secure The Human Operating System
Humans are prone to make errors. Be it just a click or forgetting to do something that needed to be done at a particular time. On top of it all, at times, companies ask their employees to bring their own devices to work. Those unsanctioned devices, an encrypted USB, a virus inflicted CD or just an employee who just wanted to use the public Wi-Fi on the company’s device to check a mail; all of these things can accumulate to a breach in a company’s cybersecurity.
Companies should educate their employees on potential baiters and phishers and encourage them to scan and verify the links they want to visit. The log-ins should be two or three stepped at least, and should require a tad bit of working before it can be accessed easily.
Default logins

Why You Should Change the Default Password on a Wi-Fi Router
A lot of times, companies overlook the default login criteria that are built-in in any and every system so that the seller can easily access the device at the time it is being sold for mock work purposes.
However, after the device is sold, the company or the IT department forgets or overlooks switching off the default setting. Consequently, if anyone checks back, he or she can easily access the data and information that the company keeps.
One fix to every problem

Better Cybersecurity Starts with Fixing Your Employees’ Bad Habits
Like mentioned before, cybersecurity and the threat towards it is very real and very present. It is continuously evolving and parties trying to breach into any and every site they want are steadily working for success.
If any company, either because they do not believe in cyber threat or just because they want to save a penny or two, only spends once in cybersecurity and doesn’t check up on it, they are practically sitting ducks.
Companies need to provide proper training to their workers and continuously upgrade their system from onlookers.