Introduction to API Security
API security is a top concern for any organization that exposes its data and services to the world. The best way to protect your API is to follow security best practices, which include using HTTPS, authentication and authorization, and input validation.
Following these best practices will help ensure that your API is secure and protected from attack.
Authentication and Authorization

API security is more important than ever. As the number of public APIs grows, so does the number of potential attack vectors. By using a few best practices, you can help protect your data and your users’ data from malicious actors.
One of the most important aspects of API security is authentication and authorization. Authentication verifies that a user is who they say they are, while authorization determines what level of access a user has to certain resources.
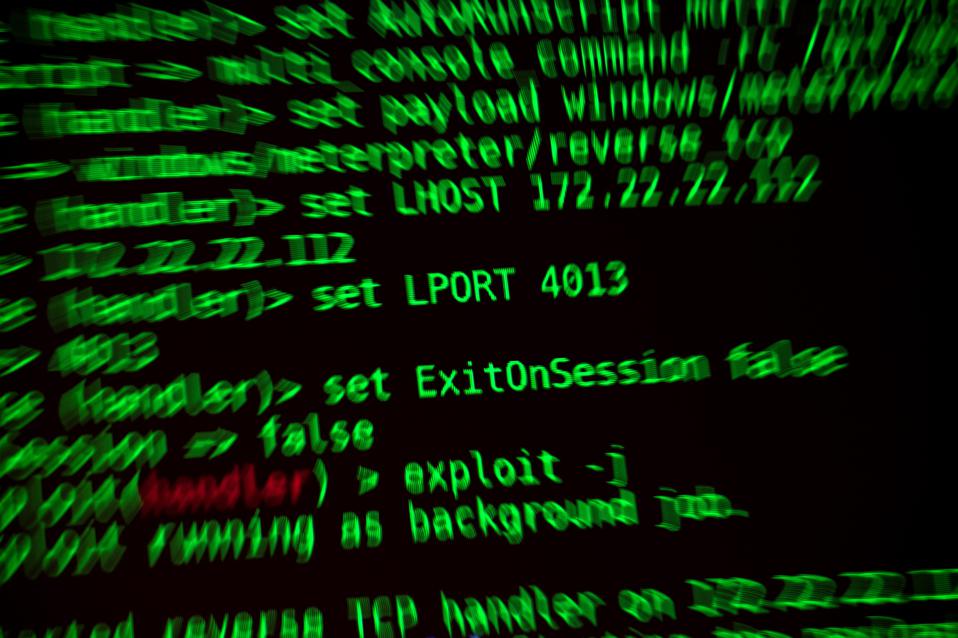
Common API Security Threats
There are many common API security threats that you should be aware of. These include injection flaws, cross-site scripting (XSS) attacks, broken authentication and session management, insufficient logging and monitoring, and security misconfiguration.
Data Protection
As more and more businesses move their data and operations online, the need for effective API security becomes more pressing. APIs are the backbone of many modern web applications, and they can provide a rich source of information for attackers.
API security is therefore essential to protecting your data from unauthorized access or modification. To protect this data, you need to carefully control who has access to it.
Authentication ensures that only authorized users can access your API. Authorization controls what actions users can perform with your API.
You should also consider encrypting all data passed through your API, both in transit and at rest. This will help protect it from being intercepted or tampered with by unauthorized parties.
Importance of Regular Security Testing
It is important to regularly test the security of your APIs. This ensures that your data is safe and secure and that your users can access the data they need. There are several ways to test the security of your APIs, but some of the most common methods involve penetration testing and code reviews.
Choosing a security platform
A cyber security platform is a centralized solution for managing and securing an organization’s data, users and network. Cybersecurity platforms enforce defensive controls, manage activities on the network, and perform configuration updates and management.
For instance, firetail is a comprehensive API security platform that can help you implement these best practices and protect your data from potential threats.
APIs are powerful tools that allow us to create robust and secure applications. However, if not implemented correctly, they can pose a security risk for your data. Proper implementation of API security best practices, along with a platform like Firetail, is essential in order to ensure the safety and integrity of your data.